According to various reports, 10-20% of the circulating supply of bitcoin is likely lost forever. However, the term "lost" in bitcoin has a different connotation than with other types of property. Technically, 100% of the issued supply of bitcoin is accounted for on the blockchain. What's really lost is access to those coins.
Below is a list of ways people frequently lose bitcoin. While they differ in many respects, most share in common compromised access—whether through physical hazard, counterparty risk, theft, or fraud. Some other pervasive risks for bitcoin loss come via user error or hubris.
1. Trading

People are often enticed by short-term trading schemes as a means of gaining quick profits which can be redeployed to acquire more bitcoin. These methods, especially the particularly risky forms using leverage or arbitrage, often lead to disappointing results for the inexperienced and a net loss of bitcoin.
Many exchanges actually encourage this behavior because it drives trading fee revenue. However, the issue with short-term trading is that markets are both unpredictable and volatile. Altcoin price swings in particular can be severe and sudden.
Because most people are influenced by their emotions when trading, they tend to make poor trading decisions—especially under stress. Over a long enough time period, the majority of amateur and even professional traders end up with less bitcoin than they would have if they'd simply accumulated over time.
2. Exchange custody risk
Cryptocurrency exchanges are the most popular way for individuals to acquire bitcoin. Given the large amount of bitcoin now held on exchanges, they are also attractive targets for attackers seeking to steal your bitcoin.
Exchanges secure users' bitcoin in a variety of ways, and are typically not very transparent about their security practices, most often allocating to you coins already held in cold storage under the exchange's control. Keeping your bitcoin in an exchange account exposes it to a variety of risks:
- Anyone gaining access to the private keys of bitcoin under the control of an exchange can steal customer funds—including cyber attackers, rogue employees, or other bad actors.
- An attacker who gains access to the login credentials of an individual's exchange account can steal funds by sending their bitcoin to an address controlled by the attacker. These attacks often involve SIM swap attacks, as we’ll discuss next.
- Because cryptocurrency exchanges are a relatively new type of legal entity, investor protections are not well established. In the event of bankruptcy or insolvency, cryptocurrency exchanges are not covered by protections such as SIPC insurance which otherwise helps traditional brokerage customers recover funds from failed companies.
- In the case of exchange insolvency, creditors of the exchange may take precedence over the exchange's customers when seeking to recover funds, resulting in the loss of customer bitcoin.
- Bitcoin held on exchanges may also risk being frozen or seized due to exchange policies or through government edict.
To avoid the basket of risks leading to the loss of bitcoin held on exchanges, the simplest solution is to transfer your bitcoin to self-custody as soon as possible after purchasing it.
3. SIM swap attacks

This risk of losing bitcoin is sometimes a subcategory of exchange risk, but it's unique enough to call out separately. Many entities, from banks to cryptocurrency exchanges, rely on SMS two-factor authentication as a means of securing customer accounts.
- In a SIM swap attack, a bad actor gains sufficient personal information about a victim to convince the victim's cell phone provider to transfer the victim's phone number to a phone controlled by the attacker.
- Sometimes, control of this phone number is all that's needed to steal credentials to an online account.
- In the case of a cryptocurrency exchange, the attacker uses credentials—often exposed in online data leaks—along with the SMS authentication to log into the victim's account and sends the victim's bitcoin to a wallet which the attacker controls.
To prevent SIM swap attacks, when available, use an authenticator app which shares a unique time-based code between your device and the service you are using. Importantly, authenticator apps are not connected with the SIM card on your phone and provide a higher degree of security beyond simple SMS verification when securing your accounts. If any of your accounts require SMS, you can also call your phone company to disable phone number porting entirely.
4. Losing your seed phrase

Losing the seed phrase is a common way people lose access to their bitcoin. A seed phrase is the embodiment of your wallet’s secrets: it generates the keys that allow you to spend your funds. If your wallet ever malfunctions, is lost, stolen, or damaged, your seed phrase enables you to restore your wallet on another device and regain access to your bitcoin.
People that lose bitcoin due to seed phrase-related issues might make one or more of these mistakes:
- Failure to properly back up a seed phrase at all
- Failure to write down the words in the correct order
- Lose their paper or metal backup
- Lose a seed phrase backed up on paper to a fire or flood
- Store a copy of the seed phrase in an insecure place—such as in a cell phone photo, cloud account, or another online medium—which, if accessed by a bad actor, leads to coins being stolen.
- Typing the seed phrase on a device infected with malware like a keylogger
Still, if you don't want to lose your bitcoin due to a misplaced, stolen, damaged, or malfunctioning device, physically back up the seed phrase to your bitcoin wallet and keep it in a safe place. This way, if you ever lose physical access to your wallet, you can restore access to your bitcoin.
5. Using a singlesig passphrase
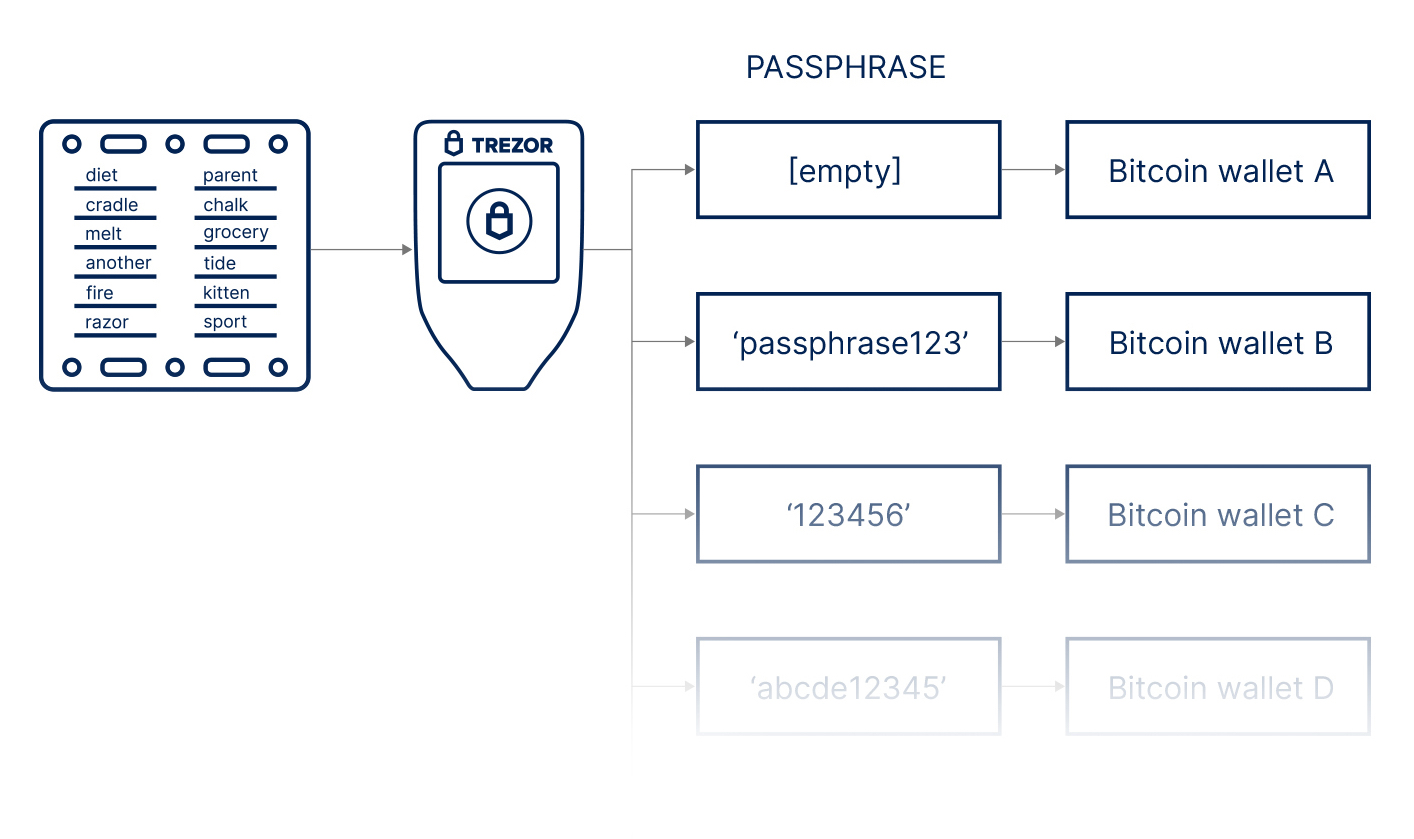
Many bitcoin wallets give you the ability to add a passphrase to your seed words to give you an extra layer of security.
Here's how they work, in short:
- Adding a passphrase is like adding a 13th or 25th seed-phrase word to your wallet.
- Passphrases contain letters, numbers, and special characters and can be up to 50 characters in length.
- Passphrases are case sensitive–so missing the capitalization of even one letter prevents access to the underlying wallet.
- Passphrases cannot be “reset” if you forget them.
Adding a passphrase gives you more security, but it comes with a trade-off. Unlike a PIN, your passphrase is critical to constructing your wallet itself. If you ever lose the passphrase or remember it incorrectly, you will lose access to your bitcoin permanently. If you use a passphrase, double-check that you record the backup of it accurately and be sure to keep the backup somewhere safe.
6. Malware
Malware is software intended to alter or damage your device for malicious purposes—including theft of bitcoin. Malware can impact phones, desktops, and web clients equally. Examples include:
- Infostealers like CryptBot that steal swaths of data from the victim’s computer, including the credentials for online accounts and bitcoin wallets
- Clipper which changes a bitcoin address either before or after being copied into your computer's clipboard from wallet software
- Cryptojacking which secretly co-opts your computer for cryptocurrency mining
- On mobile phones, third-party apps that monitor your device opening the door to sensitive information—such as logins or seed phrases—being stolen
To protect yourself from losing bitcoin due to malware, keep your device's operating system and apps up to date, ensure the apps you use came from their official sources, and review app permissions regularly. It’s always a good idea to verify addresses on hardware wallets themselves and double-check their accuracy "out of channel" (i.e., via a quick phone call, email, text message, etc.).
Ultimately, the best way to protect significant amounts of bitcoin is to upgrade your custody model: hardware wallets exist to keep your private keys separate from devices that might be infected with malware, and multisig helps eliminate single points of failure.
7. Fake bitcoin wallets
A fake bitcoin wallet scam is designed to have you download a new wallet or "update" an existing wallet to a fake wallet controlled by a scammer. It goes like this: A scammer sends a phishing "support" message claiming that your current wallet is in need of an update, and a link is provided to perform the update with cleverly mimicked screens. The next time you use the wallet, you unknowingly authorize the attacker to remove all of the funds from your wallet.
To keep from losing your bitcoin in a fake wallet scam, protect yourself by only downloading wallet software directly from the source. For mobile apps, this includes the Apple App Store or Google Play (though be careful here, as a few scammers have even breached these gatekeepers). For non-mobile apps, download wallet software directly from the vendor's official website.
8. Sending bitcoin to an incorrect address

It’s possible to lose bitcoin by sending it to the wrong address, whether that be simply pasting the wrong one or mistyping an amount to send. To prevent this, always confirm that the addresses and amounts are correct. Typing out an address manually or scanning QR codes may also help. For verification, checking the first and last four characters of an address is generally sufficient. If you use a hardware wallet, compatible devices also allow you to check deposit addresses on your device, which confirms the address you’re sending to is truly one controlled by you.
One misconception, however, is that by accidentally including a typo in a "send to" address, your bitcoin risks being sent to a non-existent address and lost forever. Most modern bitcoin wallets use a checksum to detect errors in addresses and will protect you from sending bitcoin to an invalid address—unless in a 1:4.3 billion chance (i.e., harder than winning the Powerball Lottery) you actually type in a valid address by mistake.
9. Storage media decay
This occurs when private keys or seed phrase backups are stored on media that degrades over time—also known as “bit rot”. Bit rot can occur on any device, including the device that holds your bitcoin wallet, and is caused by a variety of factors including data corruption, mechanical failure, and physical decay.
Some storage devices are more at risk from decay than others, such as HHDs being riskier than SSDs due to wear and tear on moving internal parts. That said, just about any device with storage media, including bitcoin hardware wallets, is susceptible. If the storage fails on a device you’re using, you will lose access to your bitcoin permanently.
To prevent loss of bitcoin due to bit rot, keep a physical seed phrase backup. For extra security, especially suited to stand the test of time, consider storing your seed phrase using a metal backup.
10. Phishing scams
Phishing is a form of social engineering in which a bad actor uses psychological manipulation via messages sent through email, messaging apps, text messages, or other forms of communication to convince a victim to reveal sensitive information–such as logins, passwords, pin numbers, or the seed phrase to a bitcoin wallet.
The key to protecting yourself from phishing attacks is learning how to spot phishing attempts before clicking on them or responding with sensitive information. Particularly with regard to securing your bitcoin, never reveal your seed phrase in response to an unexpected message, and when in doubt about whether there really is an issue that requires your attention, seek "out of channel verification" through a separate communication medium–such as a phone call.
Catfishing scams
If you use Twitter, Instagram, or other popular social media platforms, you’re likely familiar with catfishing. In these types of scams, impersonators, whether individuals or bots, attempt to convince you they are an influencer or well-known online personality, often creating detailed copies of the influencer's profile just to trick you.
Typically, these scammers lure you into a personal relationship, and attempt to connect with you by liking your posts, following your account, or sending you direct messages. Ultimately, they want to gain access to bitcoin wallets or request bitcoin be sent in exchange for fake services such as bitcoin trading.
The best defense in catfishing scams is healthy skepticism. Here are several techniques you can use to recognize fraudulent outreach from catfishing scammers:
- Look for subtleties in the name of the profile address such as extra or missing characters which may indicate something is out of place
- Watch for contextual clues such as improper English or unusual phrasing.
- Look at the follower count—a well-known influencer with only a few dozen followers is likely a scammer
- When available, look for a verified-user badge to confirm legitimate profiles
Grandparent, sweetheart, and other social scams

Sometimes, people lose bitcoin due to grandparent scams. In these situations, the bad actor attempts to convince a parent or grandparent that a child or relative is in some kind of trouble—and the only solution is to quickly send bitcoin. Scammers commonly recommend victims go to a bitcoin ATM, deposit cash, and subsequently transfer bitcoin to a certain address.
Bad actors often research personal information on victims from public sites, social media, dating sites, and even obituaries. They use this information in an emotional and convincing way to persuade victims into taking action. For example, an attacker might convince the victim that a loved one needs help, but is in another country and the only way to send funds quickly is via bitcoin.
Bitcoin, just like cash, offers no third-party recourse once funds change hands, so the best way to protect against these attacks is simple education on how to spot them. You can also help family custody bitcoin in such a way that coins cannot be moved without you or another custody partner countersigning a transaction.
11. Upfront deposit scams
Upfront deposit scams cause people to lose bitcoin by making use of the irreversibility of bitcoin payments. Here, an attacker lists an attractive high-priced item (i.e., like bitcoin mining equipment) for sale on a public forum, classified ad, or social media. Victims are required to send a down payment in advance to "hold" the item using bitcoin. Once the initial bitcoin is sent, both the desired item and the scammer disappear.
Protect yourself against this type of scam by never sending a down payment or paying a deposit in bitcoin unless you are absolutely certain of the reliability of your trading partner. Even then, due to the permanent nature of bitcoin payments, conditional down payments and "holding" reservations for products and other services with bitcoin should generally be avoided. In some instances, a third-party escrow service that assures the cooperation of all parties involved may offer an acceptable trade-off.
12. Ponzi schemes
In a Ponzi scheme, bitcoin is collected with the promise of yield over a certain period of time. However, the yields are usually very unrealistic. In one scam, promising 7% interest per week, the purported use of funds was for "...bitcoin arbitrage activities in order to generate returns." But the bad actor only paid "yields"—along with his own personal expenses—from bitcoin funds directly received from other depositors.
Such schemes are persuasive, in part, because interest payments initially received by investors increase confidence that the strategy is actually performing as promised. At some point, however, the party ends as the funds eventually run out, and the investor's bitcoin principal is never recovered. A variation of this approach promises yield paid in altcoin or other tokens that allegedly achieve increasing value over time. To protect yourself, the best approach is to follow the age-old advice, "If it sounds too good to be true, it probably is."
13. Using irresponsible lending platforms
Many crypto lending platforms promise you yield—anywhere from single digits to outrageous levels of return—in exchange for borrowing your bitcoin. The underlying concept can be loosely compared to buying a CD at a bank. Once popular when there were higher yields to be earned on bank accounts, banks pay you interest in exchange for the use of your funds over a certain time period (i.e., 6 months, 1 year, 2 years, etc.). If you withdraw funds early, you may pay a penalty—but such arrangements, when legitimate, provide liquidity for the bank to facilitate other forms of profitable lending.
With irresponsible lending platforms, if the platform faces counterparty risk due to overextended loans or excessive yield payment commitments, underlying bitcoin collateral is put at risk. In default, deposited bitcoin may be liquidated or claimed by creditors resulting in lost bitcoin to depositors. Also, depending on the way coins are custodied, trusting bitcoin to centralized lending platforms opens the depositor to the full array of exchange risks as explained above—including hacks, employee theft, compromised login credentials, frozen funds, and government seizures.
14. 2-for-1 schemes
This is such an obvious scam, it seems unlikely that anyone would actually fall for it. But given the number of times this ruse is attempted, it seems to work with some regularity. Here, scammers post messages saying, "Send in one bitcoin and we'll send you back two!" The obvious result is that the victim sends in one bitcoin and never hears from the scammer again.
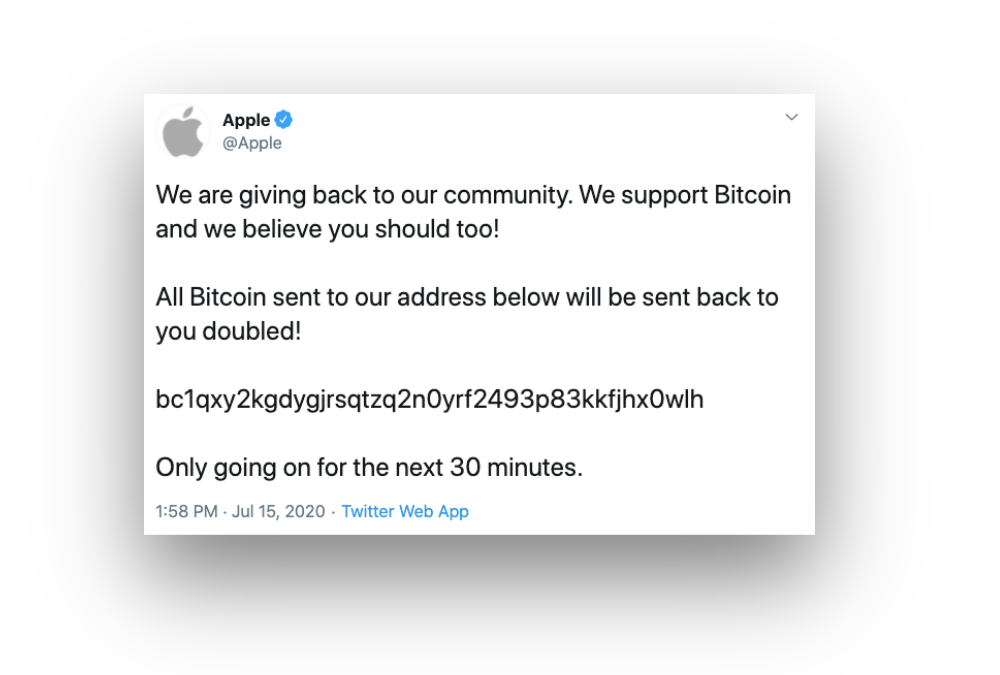
If anyone offers, "Send me one bitcoin, and I'll send you back two!", it's a scam. No one would ever legitimately offer such a trade. As mentioned in our discussion about catfishing above, the best clues, other than the offer being made in the first place, are an unverified profile, misspelled @handle, awkward "How is your trade going?" English, and an account that has far fewer followers than its legitimate counterpart would.
15. $5 wrench attacks

A “$5 wrench attack” occurs when criminals believe you have a sizable amount of bitcoin and attempt to physically coerce it from you. This risk speaks to the higher level of sovereignty bitcoin offers and its correspondingly higher demand for personal responsibility. There are a number of preventative measures you can take to limit the risk of losing your bitcoin in a $5 wrench attack, including:
- Don't talk about how much bitcoin you have
- Don't fly a bitcoin flag, wear bitcoin apparel, or put bitcoin stickers on your car or laptop
- Learn about public-record privacy for bitcoiners
- Take steps to bolster your personal security–consider a home safe, deadbolts, an alarm system, and at least one dog
- Learn about safe handling of firearms and laws related to defending your property (i.e., take a concealed carry course)
In addition to the above remedies, the best answer of all is to use a multisig storage solution with geographically distributed keys. Doing so makes it impossible to spend long-term held bitcoin from a single location and puts off potential attackers by forcing them to travel to multiple locations in order to access your funds.
16. Trusting family and friends
Bitcoin is unique in that anyone with knowledge of or access to private keys, can spend your bitcoin. As such, if you trust a family member or other third party with access to your keys, they possess the ability to spend your coins.
While there is a degree to which your closest family, such as a spouse, should ideally be aware of your bitcoin (as explained in the next section), exposing too much information to trusted family and friends can invite unwanted risks. Be careful about sharing the location of seed phrases, hardware wallets, but also information about your bitcoin custody model and the amount of bitcoin you hold.
Just because you feel you can trust someone today does not mean that you will trust them tomorrow. Some custody models like multisig allow you to share responsibility for keys while not allowing others to unilaterally control funds.
17. Poor legacy planning
While overexposure of information of bitcoin can lead to loss, so too can too much secrecy. One place this occurs is in poor legacy planning—when a bitcoin owner dies without telling close relatives that they own bitcoin or without providing heirs access to the necessary bitcoin wallets or seed phrases. Beyond these concerns, there are also legal issues with regard to inheritance planning that can impact what happens to your bitcoin.
Proper estate planning involves consulting with an attorney to establish a will, trusts, or other estate planning device(s) best suited to distribute your property upon death. For assistance with estate planning, a competent local planner can be especially helpful as estate planning rules are determined by the state in which you reside.
Once your plans are in order, you must also arrange for access to your bitcoin—often to individuals who may not understand the inner workings of bitcoin as well as you do. Multisig, especially collaborative custody, is an excellent tool for this purpose.
18. Overcomplicated security
Another way to lose your bitcoin is to get too fancy with security. Some people try encrypting their seed phrase backups digitally or splitting their seed phrase into separate physical parts—such as cutting a 12- or 24-word phrase in half and hiding each part in a different place. Others, as mentioned next, use multisig setups that require too many keys for a quorum. Still others attempt to secure funds by storing them across multiple hardware wallets and distributing many divided portions of their funds across too many obscure locations.
When security measures become overcomplicated, as in the above examples, new types of risks arise:
- Losing bitcoin because you couldn't recreate the intricate steps you created for your own backup scheme
- Losing bitcoin because you failed to communicate detailed backup plans to loved ones—or individuals you hoped to leave your bitcoin
When in doubt, stick with the basics. Private keys (i.e., derived from seeds, which are represented in human-readable form as seed phrases) are an excellent security system that even the most powerful governments in the world can't defeat. The solution is to focus on best practices for securing your private keys. From there, you can add layers of defense, such as multisig that, done properly, bolster your security without adding overly-complicated obstacles for future access to funds.
19. An unsuitable multisig quorum
With multisig wallets, a bitcoin wallet is created using multiple keys rather than a single key. Multisig wallets increase security by requiring a quorum of signatures from the keys used to create the multisig wallet to authorize future spending.

The ratio of signatures required to spend is often represented as "m-of-n" with:
- (n) being the number of keys from which the wallet was created
- (m) being the number of signatures required to spend
The quorum can be set anywhere between requiring only one of the original keys to authorize future spending, to requiring all of the keys.
Multisig is a powerful tool for securing bitcoin used by individuals, corporations, and institutions holding bitcoin savings. It is also useful for legacy planning, where in a "2-of-3" quorum, one key is held by the executor of an estate and the other by the heirs.
The risk with multisig is undershooting or overshooting the optimal ratio of keys required to spend. If you require too many keys (say, 5-of-5) from the original group and one or more of the required keys is lost, access to your bitcoin is forever lost. On the other end of the spectrum, a quorum of keys that is too low (say, 1-of-5), your funds are easy to spend and just one seed phrase or wallet being compromised would jeopardize your bitcoin.
The solution is to select an optimal ratio for your multisig quorum that balances security with a manageable level of redundancy.
20. Compromised hardware wallet
Hardware wallets are one of the best ways to secure bitcoin, but they aren't without risk. It is possible, if a bad actor were to gain access to a hardware device prior to it being activated by the end user, they could modify the device in a way that could result in a loss of bitcoin.
Hardware devices store private keys and sign transactions from within the device itself—with private keys never leaving the wallet. Devices differ in design with some using multiple internal chips and others using a single chip. If an attacker can gain physical access to the device, such as through a supply chain attack, it can be modified to change the address of outgoing transactions or pre-generate a wallet that gives the attacker access to its private keys.
To protect yourself against a compromised hardware wallet, be sure to buy your device from a trustworthy source—ideally direct from the manufacturer. Examine the packaging upon receipt to be certain it hasn't been tampered with. And, of course, store it somewhere secure and do not allow unauthorized individuals to access it.
21. Storing bitcoin in a brain wallet

Storing your bitcoin in a brain wallet is when you attempt to back up a seed phrase by memory and destroy the wallets stored on hardware devices. This makes your brain a single point of failure and can lead to not being able to remember your seed phrase for a variety of reasons, such as an unexpected injury. Additionally, if you die or become incapacitated, your bitcoin is permanently lost.
While there may be edge cases where it makes sense to do this (such as a refugee escaping an authoritarian regime at the threat of property confiscation), you should always treat bitcoin as intergenerational wealth. The solution is to not rely on your memory alone in preserving access to your bitcoin funds (i.e., see "Losing your seed phrase" above for backup methods).
The best way to protect bitcoin from loss or theft
Given all the ways to lose your bitcoin, what other steps can you take to gain peace of mind when it comes to securing your bitcoin savings? Unchained makes it easy for you to set up a multisig vault, take control of your keys, and eliminate single points of failure, all while providing the guidance you need to feel confident with your bitcoin storage.
If you’re curious about upgrading your bitcoin security, Unchained offers a consultation to chat through your options, with no strings attached. Unchained’s team of experts will be happy to explain what the setup process looks like and answer any questions you may have about taking control of and safely storing your bitcoin keys.


.png)